Transparent data encryption
Transparent data encryption (TDE) protects at rest data. TDE requires a secure local file system to be effective.
Transparent data encryption (TDE) protects at rest data. At rest data is data that has been stored on disk.
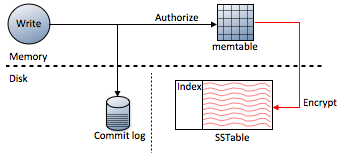
As shown in the diagram, data stored in the commit log is not encrypted. If you need commit log encryption, store the commit log on an OS-level encrypted file system using a security product such as Vormetric. Data can be encrypted using different algorithms, or not at all. SSTable data files are immutable after they have been flushed to disk and encrypted only once when they are written to disk.
The Cassandra File System (CFS) is accessed as part of the Hadoop File System (HDFS) using the configured authentication. If you encrypt the CFS keyspace's sblocks and inode tables, all CFS data is encrypted.
Data that is not encrypted
- Table partition key and clustering columns
- Database files other than the commit log and SSTable data files
- Spark spill files
Requirements
TDE requires a secure local file system to be effective. Encryption certificates are stored off-server with KMIP encryption or locally with on-server encryption.
To get the full capabilities of TDE, download and install the Java Cryptography Extension (JCE), unzip the jar files and place them under $JAVA_HOME/jdk/lib/security. JCE-based products are restricted for export to certain countries by the U.S. Export Administration Regulations.
TDE limitations and recommendations
Data is not directly protected by TDE when you access the data using the following utilities:
| Utility | Reason utility is not encrypted |
|---|---|
| json2sstable | Operates directly on the SSTables. |
| nodetool | Uses only JMX, so data is not accessed. |
| sstable2json | Operates directly on the SSTables. |
| sstablekeys | Operates directly on the SSTables. |
| sstableloader | Operates directly on the SSTables. |
| sstablescrub | Operates directly on the SSTables. |
Compression and encryption introduce performance overhead.
