Functions and Aggregate Resources
Locate the cassandra.yaml file. The location of this file depends on the type of installation:
-
Package installations:
/etc/dse/cassandra/cassandra.yaml -
Tarball installations:
<installation_location>/resources/cassandra/conf/cassandra.yaml
The function syntax applies to user-defined functions and aggregates. Although user-defined functions and aggregates are located in a keyspace, function permissions are distinct and must be applied separately.
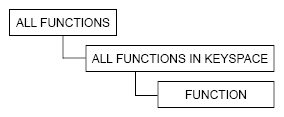
Access is controlled using modeled hierarchy. Granting and revoking a privilege on a top-level object automatically allows the same permission on all descendants (child objects under the top-level object).
Restriction: User defined functions are only available in environments that have enable_user_defined_functions set to true in the cassandra.yaml file.
Locate the cassandra.yaml file. The location of this file depends on the type of installation:
-
Package installations:
/etc/dse/cassandra/cassandra.yaml -
Tarball installations:
<installation_location>/resources/cassandra/conf/cassandra.yaml
Functions have the following hierarchy.
Synopsis
Use the following syntax to control access to functions:
-
ALL FUNCTIONSsyntax:GRANT <privilege_list> ON **ALL FUNCTIONS** TO <role_name>;where the privileges are ALL PERMISSIONS, ALTER, CREATE, DROP, and EXECUTE
-
ALL FUNCTIONS IN KEYSPACEsyntax:GRANT <privilege_list> ON **ALL FUNCTIONS IN KEYSPACE <keyspace_name>** TO <role_name>;where the privileges are ALL PERMISSIONS, ALTER, CREATE, DROP, and EXECUTE
-
FUNCTIONsyntax:GRANT <privilege_list> ON **FUNCTION <function_name> ( <argument_types> ) ** TO <role_name>;where the function name is fully qualified and the privileges are ALL PERMISSIONS, ALTER, DROP, and EXECUTE
-
REVOKEsyntax:REVOKE <permission_list> ON resource FROM role_name;
Permission matrix
When a permission is granted to a role, users are able to perform the corresponding operations.
| privilege_name | resource_name | Permissions |
|---|---|---|
ALL FUNCTIONS |
All operations (ALTER, CREATE, DROP, and EXECUTE permissions) on all functions in all keyspaces. |
|
ALL FUNCTIONS IN KEYSPACE |
All operations (ALTER, CREATE, DROP, and EXECUTE) on all functions in the selected keyspace. |
|
FUNCTION |
All operations (ALTER, DROP, and EXECUTE) on the selected function. |
|
ALL FUNCTIONS |
CREATE OR REPLACE FUNCTION and CREATE OR REPLACE AGGREGATE on existing functions in all keyspaces. |
|
ALL FUNCTIONS IN KEYSPACE <keyspace_name> |
CREATE OR REPLACE FUNCTION and CREATE OR REPLACE AGGREGATE on existing functions in a specific keyspace. |
|
FUNCTION <function_name> |
CREATE OR REPLACE FUNCTION and CREATE OR REPLACE AGGREGATE on an existing function. |
|
ALL FUNCTIONS |
CREATE FUNCTION and CREATE AGGREGATE in all keyspaces. |
|
ALL FUNCTIONS IN KEYSPACE <keyspace_name> |
CREATE FUNCTION and CREATE AGGREGATE in specified keyspace. |
|
ALL FUNCTIONS |
DROP FUNCTION and DROP AGGREGATE in all keyspaces. |
|
ALL FUNCTIONS IN KEYSPACE <keyspace_name> |
DROP FUNCTION and DROP AGGREGATE in specified keyspace. |
|
FUNCTION <function_name> |
DROP FUNCTION or DROP AGGREGATE specified function. |
|
ALL FUNCTIONS |
Use a function or aggregate in SELECT, INSERT, and UPDATE in all keyspaces. Create an aggregate that contains a function. |
|
ALL FUNCTIONS IN KEYSPACE <keyspace_name> |
Use a function or aggregate in SELECT, INSERT, and UPDATE in a keypsace. Create an aggregate that contains a function in the keyspace. |
|
FUNCTION <function_name> |
SELECT, INSERT and UPDATE using specified function and use of the function in CREATE AGGREGATE. |
