Managing DSE Security using LCM
Authentication for DataStax Enterprise clusters is enabled by default in a Lifecycle Manager configuration profile.
opscenterd.conf
The location of the opscenterd.conf file depends on the type of installation:- Package installations: /etc/opscenter/opscenterd.conf
- Tarball installations: install_location/conf/opscenterd.conf
Authentication
Authentication for DataStax Enterprise clusters is enabled by default in a Lifecycle Manager configuration profile. Configuration profiles created for supported DSE versions earlier than DSE version 5.0 enable the PasswordAuthenticator option by default. Configuration profiles created for DSE version 5.0 and later use the DSE Authenticator by default: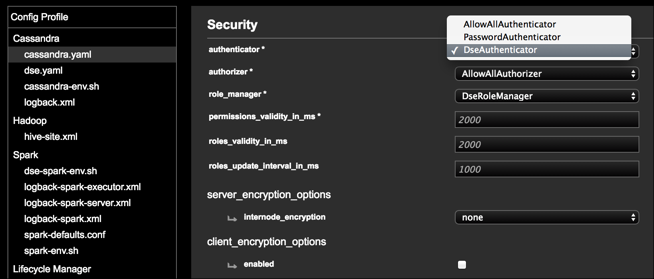
Node-to-Node Encryption
Lifecycle Manager can configure DataStax Enterprise clusters to use node-to-node encryption. The feature is disabled by default. See Configuring SSL/TLS for DSE using LCM for step-by-step instructions for enabling internode encryption using LCM Config Profiles.
When internode_encryption is enabled (by selecting a value of all, dc, or rack in the Security panel of cassandra.yaml in Config Profile), Lifecycle Manager automates the process of setting up SSL certificates using an internal certificate authority and deploys the resulting keystore and truststore to each node automatically. No further action is necessary beyond running an install or configure job.
Client-to-Node Encryption
Lifecycle Manager can configure DataStax Enterprise clusters to use client-to-node encryption. The option is disabled by default. See Configuring SSL/TLS for DSE using LCM for step-by-step instructions for enabling client encryption using LCM Config Profiles.
When client-to-node encryption is enabled (by selecting enabled for client_encryption_options in the Security panel of cassandra.yaml in Config Profile), Lifecycle Manager automates the process of preparing server certificates, exactly as it does for node-to-node encryption.
Some organizations might not want to use the internal certificate authority in Lifecycle Manager, and can manually deploy the keystore and truststore as described for node-to-node encryption.
- If certificates were generated by the internal certificate authority in Lifecycle Manager, download the CA certificate.
- If certificates were generated outside of Lifecycle Manager, acquire the appropriate CA certificate or self-signed certificates. See Using non-LCM generated certificates.
Internal Certificate Authority generated by LCM
- When Lifecycle Manager is first started, it creates a self-signed 2048 bit RSA
certificate authority that is stored in the
[lifecycle_manager].cacerts_directoryin opscenterd.conf. - When running install or configure jobs, Lifecycle Manager generates a keystore and truststore for each node if necessary. Certificate generation occurs if either node-to-node or client-to-node encryption is enabled, and if there is no pre-existing keystore or truststore in the locations specified by the configuration profile.
- When generating a keystore for each node, Lifecycle Manager creates a certificate signing request for the node, signs the request with the internal certificate authority, and packages the resulting certificate in a JKS-formatted keystore.
- When generating a truststore for each node, Lifecycle Manager packages the CA certificate in a JKS-formatted truststore. The same CA is used to sign certificates for all nodes in all clusters, and it enables validation of all automatically generated certificates.
Using non-LCM generated certificates
- Prior to running an install or configure job, prepare keystores and truststores for each node outside of Lifecycle Manager.
- Deploy the appropriate keystore and truststore to each DataStax Enterprise server using scp, rsync, or some other method of file deployment. The keystore files are commonly deployed to the /etc/dse/keystores/ directory.
- Edit the config profile in Lifecycle Manager so that the keystore and truststore paths point to the location where the files were deployed as mentioned above; for example /etc/dse/keystores/server.keystore and /etc/dse/keystores/server.truststore.
- Edit the config profile in Lifecycle Manager so that the keystore and truststore passwords allow DataStax Enterprise to unlock the files that were manually deployed.
- Run an install or configure job. When executing the job, Lifecycle Manager configures each DataStax Enterprise server to use the pre-deployed keystore and truststore you have provided. Lifecycle Manager does not attempt to prepare certificates using the internal certificate authority when it finds a pre-existing keystore and truststore present on a DataStax Enterprise server.