Configuring SSL/TLS for DSE using LCM
Configure SSL/TLS for a DSE cluster using Lifecycle Manager Config Profile. This is the recommended procedure for a production environment. Follow these steps to enable node-to-node and client-to-node encryption.
- Client-to-node encryption is enabled by default, and can use certificates generated by the internal certificate authority in LCM, or certificates generated outside of LCM.
- Node-to-node encryption is enabled by default, but can be configured by enabling internode communication.
When either node-to-node or client-to-node encryption is enabled, LCM creates keystores and truststores for DSE node-to-node and client-to-node SSL/TLS communication with the following default names and locations:
- /etc/dse/keystores/client.keystore (client-to-node keystore)
- /etc/dse/keystores/client.truststore (client-to-node truststore)
- /etc/dse/keystores/server.keystore (node-to-node keystore)
- /etc/dse/keystores/server.truststore (node-to-node truststore)
[agents]
ssl_keystore_password = cassandra
ssl_keystore = /etc/dse/keystores/client.keystore
[cassandra]
ssl_keystore_password = lifecyclemanager
ssl_keystore = /var/lib/opscenter/ssl/lcm/lcm-auto-generated.truststoreThe keystore file used for DataStax Agents to communicate with DSE nodes is exactly the same as that used by a DSE node connecting to other DSE nodes.
The keystore file used for the OpsCenter daemon communicating with DSE nodes is automatically generated by the LCM configuration process and put under the folder /var/lib/opscenter/ssl/lcm.
For information about manually configuring cluster connections (using the OpsCenter UI), see Editing OpsCenter cluster connections for authentication or encryption.
cluster_name.conf
The location of the cluster_name.conf file depends on the type of installation:- Package installations: /etc/opscenter/clusters/cluster_name.conf
- Tarball installations: install_location/conf/clusters/cluster_name.conf
Prerequisites
Procedure
- Click Config Profiles from the Lifecycle Manager navigation menu.
- Click the edit icon for the configuration profile to edit, or click Add config profile if you have not already created a profile.
-
In the Config Profile pane under the
Cassandra section, select
cassandra.yaml.
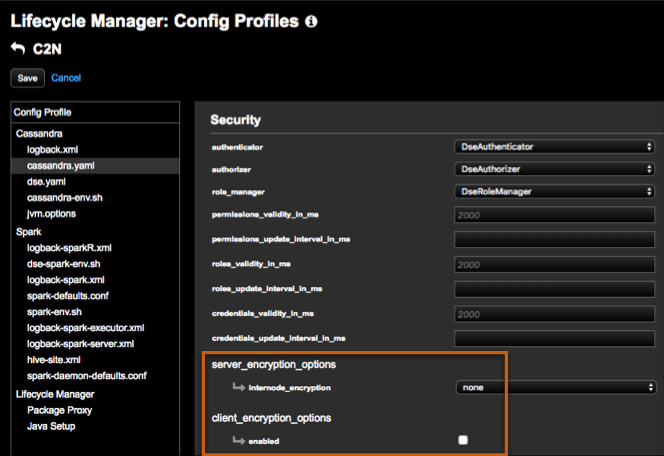
-
In the Security pane under
server_encryption_options, select one of the
following options for internode_encryption.
- all: All inter-node communication is encrypted. (Recommended and strongest option.)
- dc: Traffic between datacenters is encrypted. Select this option if there is concern about a performance impact of encrypting traffic locally, but encryption is still required for inter-datacenter traffic that might transit untrusted links.
- rack: Traffic between racks is encrypted.
Tip: For more details about available configuration options, see /en/dse/6.0/dse-admin/datastax_enterprise/config/configCassandra_yaml.html#configCassandra_yaml__server_encryption_options. - Re-enter keystore and truststore passwords for confirmation.
-
In the Security pane, select the
enabled option for
client_encryption_options.
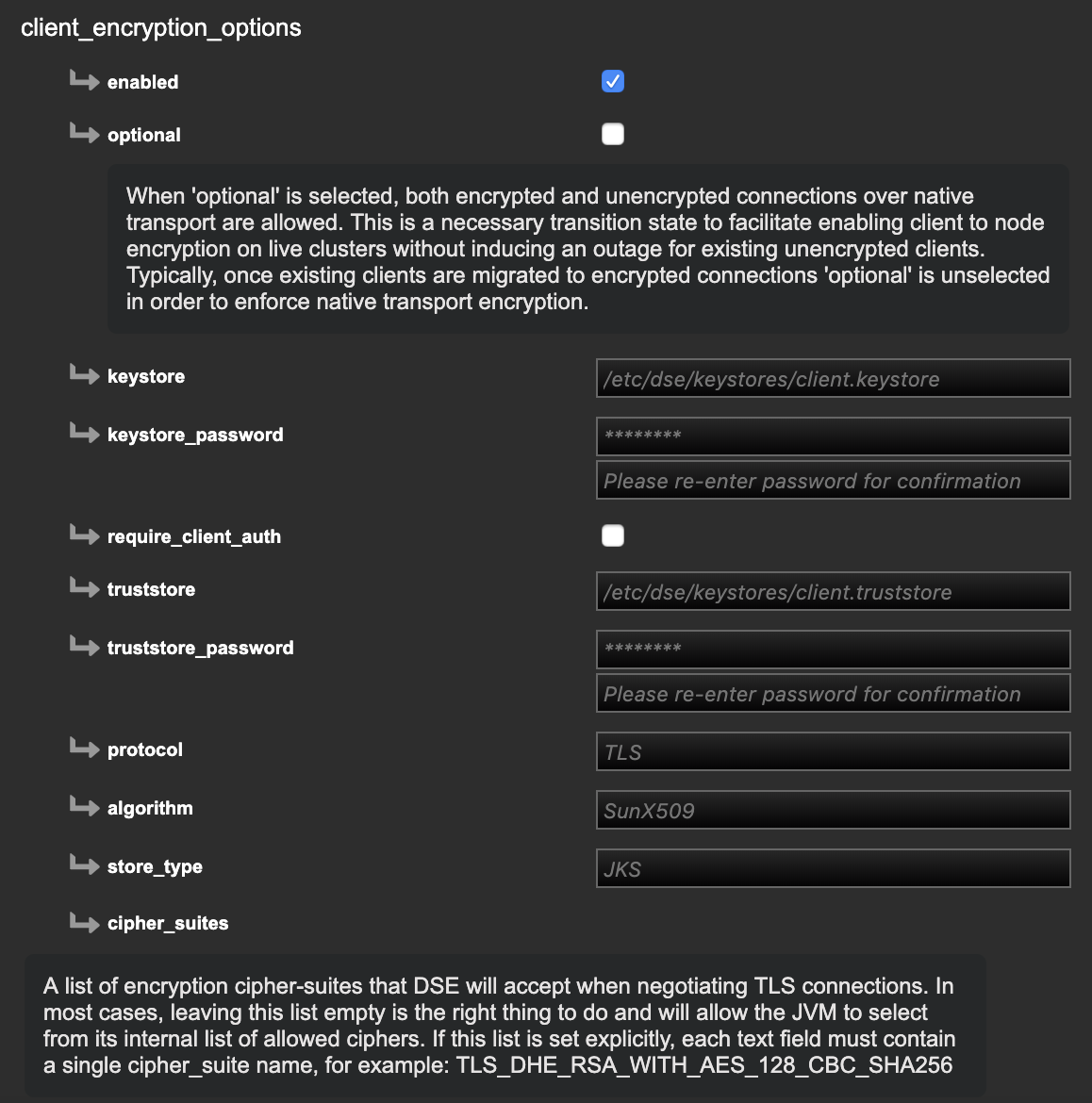 Tip: For more details about available configuration options, see /en/dse/6.0/dse-admin/datastax_enterprise/config/configCassandra_yaml.html#configCassandra_yaml__client_encryption_options.
Tip: For more details about available configuration options, see /en/dse/6.0/dse-admin/datastax_enterprise/config/configCassandra_yaml.html#configCassandra_yaml__client_encryption_options. - Re-enter keystore and truststore passwords for confirmation.
- Click Save to save the Config Profile.
What's next
- Go to the Clusters workspace in Lifecycle Manager and select the configuration profile to apply at the cluster level.
- If an install job has not been run yet on the cluster, Run an Install Job. Otherwise, Run a configure job to apply the configuration profile changes.
- Monitor the job. When the job completes successfully, SSL/TLS setup for the DSE cluster is enabled.
- Download the generated CA cert for use with the DSE client SSL connection.
