About Internal authentication
Internal authentication is based on Cassandra-controlled roles and passwords.
Like many databases, Cassandra uses rolenames and passwords for internal authentication. Role-based authentication encompasses both users and roles to bring a number of useful features to authorization. Roles can represent either actual individual users or roles that those users have in administering and accessing the Cassandra cluster.
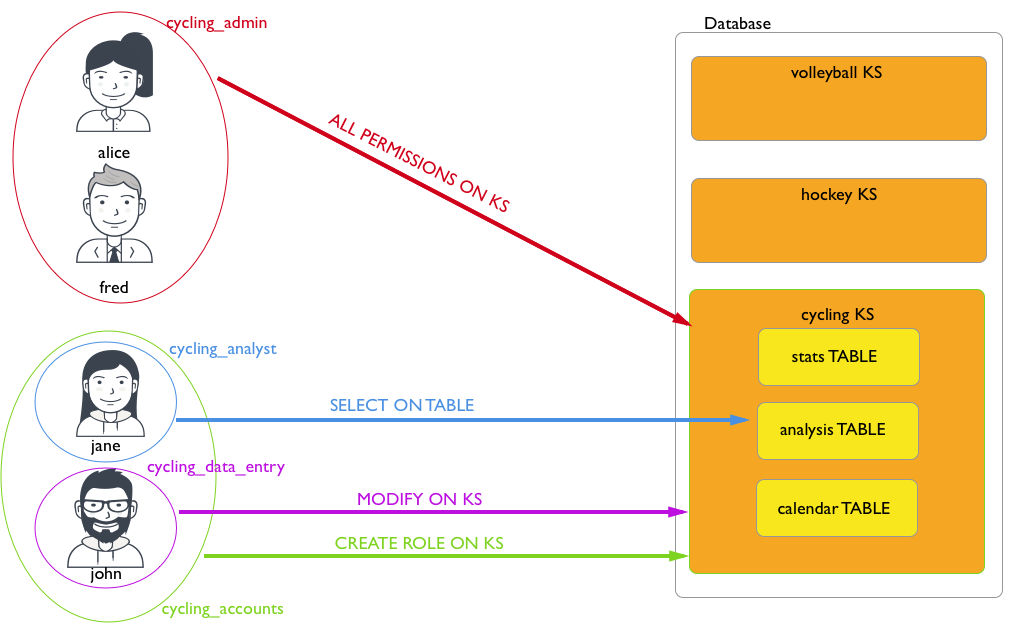
For example, a user named alice is created and given login
privileges:
CREATE ROLE alice WITH PASSWORD = 'enjoyLife' AND LOGIN = true;CREATE ROLE cycling_admin WITH PASSWORD = '1234abcd';
GRANT ALL PERMISSIONS ON KEYSPACE cycling TO cycling_admin;GRANT cycling_admin TO alice;CREATE ROLE cycling_analyst WITH PASSWORD = 'zyxw9876';
GRANT SELECT ON TABLE cycling.analysis TO cycling_analyst;
CREATE ROLE hockey_analyst WITH PASSWORD = 'Iget2seeAll';
GRANT SELECT ON TABLE hockey.analysis TO hockey_analyst;
GRANT hockey_analyst TO cycling_analyst;
GRANT cyclist_analyst TO jane;Note: Permissions and
An important change that roles-based access control also introduces is that
the need for SUPERUSER status are inherited, but the LOGIN privilege
is not.SUPERUSER privileges in order to perform user/role management
operations is removed. A role can be authorized to create roles or be authorized to grant and
revoke
permissions:// Give cycling_accounts the right to create roles
GRANT CREATE ON ALL ROLES TO cycling_accounts;
// Give cycling_accounts the right to grant or revoke permissions
GRANT AUTHORIZE ON KEYSPACE cycling TO cycling_accounts;
GRANT cyclist_accounts TO jane;
GRANT cyclist_accounts TO john;Internal authentication and authorization information is stored in the
following Cassandra tables:
- system_auth.roles
- Table that stores the role name, whether the role can be used for login, whether the role is a superuser, what other roles the role may be a member of, and a bcrypt salted hash password for the role.
- system_auth.role_members
- Table that stores the roles and role members.
- system_auth.role_permissions
- Table that stores the role, a resource (keyspace, table), and the permission that the role has to access the resource.
- system_auth.recqlshSourceole_permissons_index
- Table that stores the role and a resource that the role has a set permission.
Once roles and passwords have been set, Cassandra can be configured to use authentication in the cassandra.yaml file.
The location of the cassandra.yaml file depends on the type of installation:
| DataStax Enterprise 5.0 Installer-Services and package installations | /etc/dse/cassandra/cassandra.yaml |
| DataStax Enterprise 5.0 Installer-No Services and tarball installations | install_location/resources/cassandra/conf/cassandra.yaml |
| Cassandra package installations | /etc/cassandra/cassandra.yaml |
| Cassandra tarball installations | install_location/resources/cassandra/conf/cassandra.yaml |
If roles exist and Cassandra is configured to use authentication, Cassandra tools must be executed with optional authentication options.
- cqlsh with authentication
- DevCenter authenticated connections
- DataStax drivers - produced and certified by DataStax to work with Cassandra.
