Editing OpsCenter cluster connections for authentication or encryption
Cluster connection settings define how OpsCenter connects to a DSE cluster. Edit the cluster connection settings if authentication or encryption has been enabled on a DSE cluster.
cluster_name.conf
The location of the cluster_name.conf file depends on the type of installation:- Package installations: /etc/opscenter/clusters/cluster_name.conf
- Tarball installations: install_location/conf/clusters/cluster_name.conf
Procedure
- Select the cluster to edit from the Cluster menu in OpsCenter Monitoring.
-
Click .
The Edit Cluster Connection Settings dialog appears.
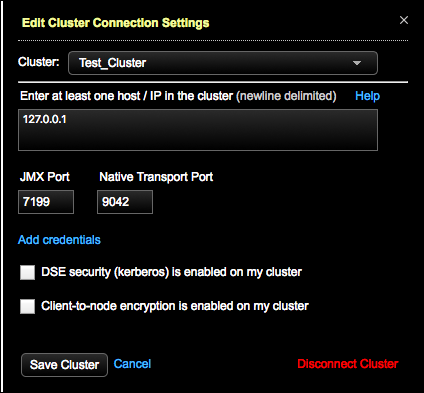 Tip: Select other clusters to edit connection settings for from the Cluster list.
Tip: Select other clusters to edit connection settings for from the Cluster list. - If applicable, change the IP addresses of cluster nodes.
- If applicable, change the JMX Port and Native Transport Port listen port numbers if you are not using the defaults.
- If applicable, click Add credentials to add or edit the user credentials (username and passwords) if the JMX or Native Transport ports require authentication.
- Optional:
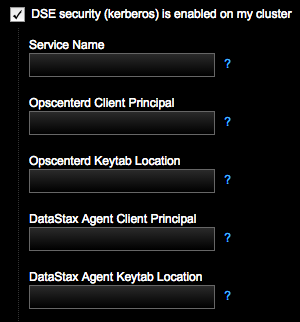
If applicable to your environment, select DSE security (kerberos) is
enabled on my cluster and complete the fields.
-
Enter the Service Name.
For example, if the server principal on your nodes is
dse/nodeX.your_domain.com@your_domain.com, this field should bedse. -
Enter the Opscenterd Client
Principal for the OpsCenter process/machine to use. The
service principal name for OpsCenter is
opscenterd/opscenter_node_fqdn, where fqdn is the Fully Qualified Domain Name. Example: opscenterd/opscenterd.your_domain.com. -
Enter the location of the keytab OpsCenter
machine in Opscenterd Keytab Location, which
contains credentials for the
opscenter_client_principal. Example:/etc/opscenter/secuirty/krb5_opsc.keytab. -
Enter the client principal for the DataStax Agent
process/machine to use in DataStax Agent Client
Principal. The service principal name for the
datastax-agent node is
dxagent/datastax-agent_node_fqdn, where fqdn is the Fully Qualified Domain Name. Example: dxagent/_HOST. -
Enter the location of the keytab on the DataStax
Agent machines in DataStax Agent Keytab Location,
which contains credentials for the
agent_client_principal. Example: /var/lib/datastax-agent/krb5_agent.keytab.
For more information, see Setting up Kerberos and the Kerberos tutorial.
-
Enter the Service Name.
For example, if the server principal on your nodes is
-
If configuring client-to-node settings, select
Client-to-node encryption is enabled on my cluster.
Indicate the following paths for OpsCenter and each agent to use for connecting
directly to the monitored DSE cluster.
 Note: For information about creating keystores and truststores, see Enabling client-to-node encryption in OpsCenter.
Note: For information about creating keystores and truststores, see Enabling client-to-node encryption in OpsCenter. -
If configuring client-to-node settings, indicate the following for OpsCenter
and each agent to use for connecting directly to the monitored DSE
cluster.
When client-to-node encryption is enabled for a cluster using Lifecycle Manager, the
ssl_truststoreandssl_truststore_passwordfields are automatically propagated in cluster_name.conf with the corresponding values fromssl_keystoreandssl_keystore_passwordfor both opscenterd and the DataStax Agent.LCM propagates the
ssl_keystorevalue intossl_keystoreandssl_truststore, and thessl_keystore_passwordvalue intossl_keystore_passwordandssl_truststore_password.-
Enter the OpsCenter Keystore Path, which is the
SSL keystore location for OpsCenter (opscenterd) to use for connecting
to the monitored DSE cluster. The value entered in the UI populates the
[cassandra] ssl_keystoreproperty in the OpsCenter cluster configuration file (cluster_name.conf). -
Enter the Password for the OpsCenter
Keystore Path. The value entered in the UI populates the
[cassandra] ssl_keystore_passwordproperty in cluster_name.conf. -
Enter the OpsCenter Truststore Path, which is
the SSL truststore location for OpsCenter (opscenterd) to use for
connecting to the monitored DSE cluster. This value should be the same
as OpsCenter Keystore Path if the same file is
used as both the keystore and the truststore (that is, there is not a
separate truststore). The value entered in the UI populates the
[cassandra] ssl_truststoreproperty in cluster_name.conf. -
Enter the Password for the OpsCenter
Truststore Path. This value should be the same as
password for the OpsCenter Keystore Path if the
same file is used as both the keystore and the truststore (that is,
there is not a separate truststore). The value entered in the UI
populates the
[cassandra] ssl_truststore_passwordproperty in cluster_name.conf. -
Enter the Agent Keystore Path, which is the SSL
keystore location for each agent to use for connecting to the monitored
DSE cluster. The value entered in the UI populates the
[agents] ssl_keystoreproperty in cluster_name.conf. -
Enter the Password for the Agent
Keystore Path. The value entered in the UI populates the
[agents] ssl_keystore_passwordproperty in cluster_name.conf. -
Enter the Agent Truststore Path, which is the
SSL truststore location for each agent to use for connecting to the
monitored DSE cluster. This value should be the same as password for the
Agent Keystore Path if the same file is used
as both the keystore and the truststore (that is, there is not a
separate truststore).The value entered in the UI populates the
[agents] ssl_truststoreproperty in (cluster_name.conf). -
Enter the Password for the Agent
Truststore Path. This value should be the same as
password for the Agent Keystore Path if the same
file is used as both the keystore and the truststore (that is, there is
not a separate truststore). The value entered in the UI populates the
[agents] ssl_truststore_passwordproperty in cluster_name.conf.
-
Enter the OpsCenter Keystore Path, which is the
SSL keystore location for OpsCenter (opscenterd) to use for connecting
to the monitored DSE cluster. The value entered in the UI populates the
- Click Save Cluster.
