Configuring row-level access control
Enable row-level access control (RLAC) in LCM for DSE clusters that have tables with row-level permissions required for user access.
Row-level access control (RLAC) enforces an organization's authorization policies to data within a table by matching a filter, such as a user or company name, applied to a text-based partition key. RLAC provides more granular security for tables so that only authorized users are able to view or modify subsets of the data. The RLAC feature is useful for multi-tenant applications.
Enable row-level access control in LCM for DSE clusters that have tables with
row-level permissions required for access. Follow these steps to make Lifecycle
Manager (LCM) aware of and allow use of RLAC configured for DSE clusters provisioned
and managed by LCM.
Note: RLAC is supported in DSE 5.1 and later, and LCM
6.1 and later.
Procedure
- Click Config Profiles from the Lifecycle Manager navigation menu.
- Click the edit icon for the config profile you want to edit, or click Add config profile if you have not already created a profile.
-
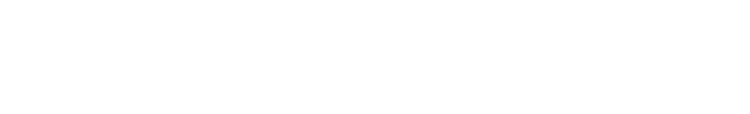
In the Config Profile pane under the Cassandra section,
click cassandra.yaml. In the
Security pane:
- Ensure that the authenticator setting is DseAuthenticator.
- Ensure that the authorizer setting is DseAuthorizer.
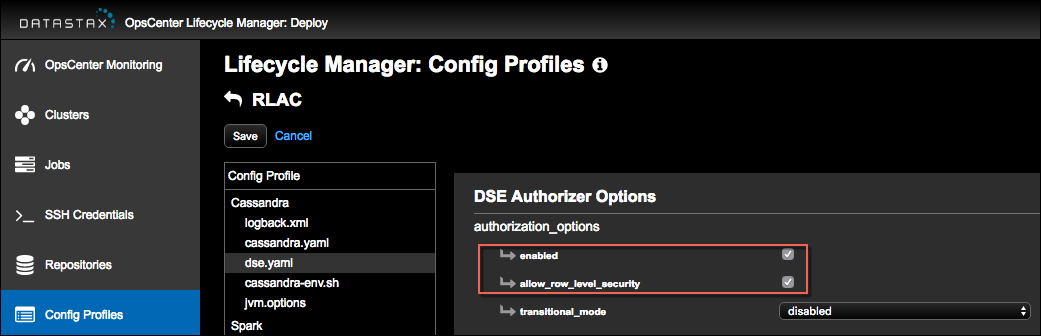
- In the Config Profile pane under the Cassandra section, click dse.yaml.
-
Scroll to the DSE Authorizer Options pane.
- Select enabled for authorization options.
- Select allow_row_level_security.
- Click Save to save the Config Profile.
What's next
- Go to the Clusters workspace in Lifecycle Manager and select the config profile to apply at the cluster, datacenter, or node level. Nodes can inherit config profile settings from the cluster or datacenter levels, or have settings at the node level that take precedence.
- Run a configuration job to push the configuration to all of the applicable nodes.
- Restrict the applicable tables rows and grant permissions to the applicable role names using GRANT or REVOKE statements as required for your environment. For details, see Setting row-level permissions in the DSE Administrator documentation.
- Log in as each user role and run queries to confirm that results represent your defined access permissions. See an example.