To enable SSL for package installations, you edit the configuration file and run a
script to generate the keys used by OpsCenter and the agents.
opscenterd.conf
The location of the opscenterd.conf file depends on the type of
installation:
| Location |
Package |
Installer (GUI or text mode) |
Tarball |
| Service |
No-service |
| /etc/opscenter/opscenterd.conf |
X |
X |
|
|
| install_location/conf/opscenterd.conf |
|
|
X |
X |
address.yaml
The location of the address.yaml file depends on the type of
installation:
- Package installations:
/var/lib/datastax-agent/conf/address.yaml
- Tarball installations:
install_location/conf/address.yaml
Prerequisites
- The Python interface for the OpenSSL library (pyOpenSSL).
With package installs (rpm or deb) of OpsCenter, the
python-openssl package is installed as a dependency.
However, this is not the case with CentOS 5.x installs.
Procedure
-
Ensure that a version of pyOpenSSL
compatible with the version of libssl installed is a
requirement for any secure communications in OpsCenter.
- OpsCenter ships with pyOpenSSL 0.10, compiled for
libssl 0.9.8, so if you are using
libssl 0.9.8 on the machine running
opscenterd, no further action should be
required.
- If you are using libssl 1.x, you need to ensure that
pyOpenSSL 0.10+ is installed and compiled
properly.
-
(Optional) Determine the version of pyOpenSSL
installed.
$ python -c "import OpenSSL; print OpenSSL.__version__"
-
(Optional) Manually install pyOpenSSL.
$ sudo easy_install pyOpenSSL
-
Run the OpsCenter setup.py script:
$ sudo /usr/share/opscenter/bin/setup.py
The script generates the SSL keys and certifcates used by the OpsCenter
daemon and the agents to communicate with one another in the following
directory.
/var/lib/opscenter
-
Open in an editor and add two
lines to enable SSL.
$ sudo vi /etc/opscenter/opscenterd.conf
[agents]
use_ssl = true
-
Restart the OpsCenter daemon.
If you want to connect to a cluster in which agents have already been
deployed, you can log in to each of the nodes and reconfigure the
file (see steps below).
-
Reconfigure the agents on all nodes.
-
Copy /var/lib/opscenter/ssl/agentKeyStore from the
OpsCenter machine to
/var/lib/datastax-agent/ssl/agentKeyStore on
each node in the cluster.
$ scp /var/lib/opscenter/ssl/agentKeyStore user@node:/var/lib/datastax-agent/ssl/
Where
node is either the host name of the node or its
IP address and
user is the userid on the
node.
-
Log into each node in the cluster using ssh.
-
Edit the address.yaml file, changing the value of
use_ssl to 1.
$ sudo vi /var/lib/datastax-agent/conf/address.yaml
use_ssl: 1
-
Restart the agent.
$ sudo service datastax-agent restart
If you do not want to edit all the node
configuration files by hand, you can follow the agent installation
procedure.
-
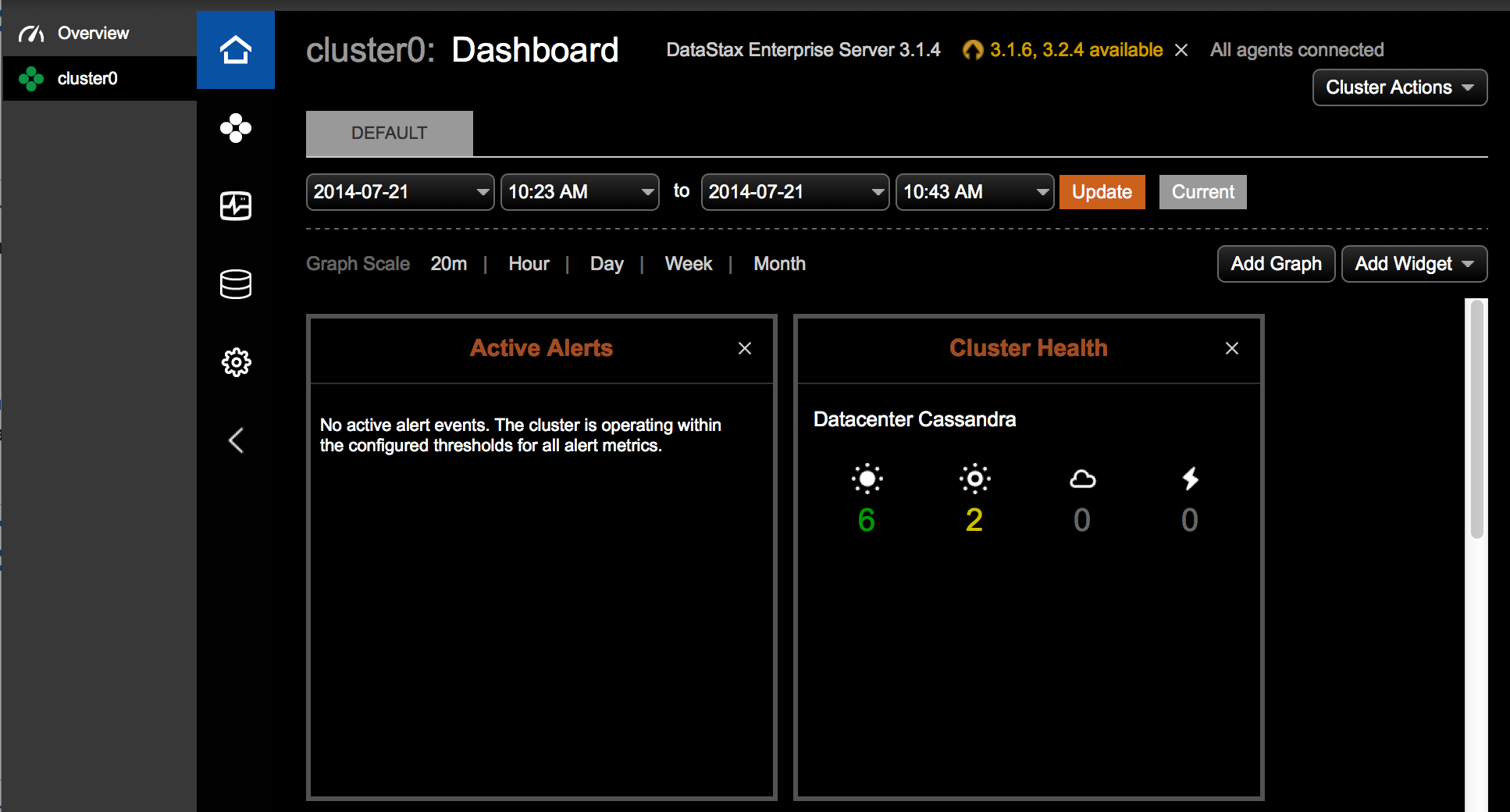
Once opscenterd and all agents have been configured and
restarted, verify proper connection via the dashboard.